Stuxnet is a working and fearsome prototype of a cyber-weapon that will lead to the creation of a new arms race in the world
Kaspersky Labs
When one of the world’s leading malware research labs releases a quote like this, it’s time to get worried. Stuxnet is one of the most advanced pieces of computer malware ever, and it’s working in ways security experts never thought malware could.
A computer worm is a type of virus which spreads itself from machine to machine, with the sole purpose of reproducing. One of the most famous examples of this is the SQL Slammer worm, which managed to bring the Internet to a halt in early 2002. While a worm itself might not be malicious, they often carry a “payload,” another piece of malware which contains the malicious code that reproduces with the worm. Typically worms, trojans, and other malware have targeted home and business computers. While many are harmless—and sometimes even playful—the worst can result in computer crashes, lost data, or stolen personal information.
Don’t turn off your computer just yet. Stuxnet isn’t interested in stealing credit cards; it’s potentially much more dangerous. Stuxnet targets machines used in industrial processes, like those in nuclear reactors and manufacturing plants, allowing the virus writers to reprogram these systems. Stuxnet conceals itself by hiding changes from plant operators.
Stuxnet duplicates itself through intranet connections—local networks and portable storage devices—by exploiting four previously unnoticed security holes in the Windows operating system. Worms usually exploit only one hole, saving the others for future attacks. Upon infection, Stuxnet investigates the host machine, looking for Siemens software used in industrial machines. Stuxnet then takes control of the computers, thereby controlling industrial processes. The virus is capable of reprogramming the programmable logic control device of the computer—the core of an industrial machine.
Upon hijacking a machine, Stuxnet reports back to a central server for further instructions. Besides attacking unusual targets, Stuxnet also includes many features not often seen in malware: digital signing, multiple programming languages, knowledge of industrial processes, and use of multiple zero-day exploits.
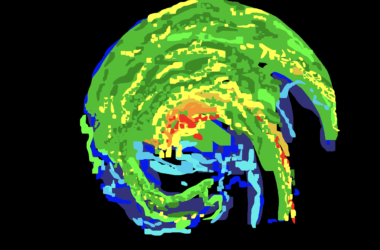
The worm has spread quickly in Iran, where an estimated 60 per cent of computers are infected. Elsewhere in the world, the worm is less widespread, suggesting that the initial infection started in Iran. Experts have hypothesized that the attackers are targeting the country in an attempt to sabotage its nuclear reactors. The virus was likely created by a team of hackers and took years to create. This level of dedication and sophistication in creating malware has never been seen before and suggests that the folks behind the virus have serious intentions (they also probably had insiders and experts on their side). Security experts say there is little chance of catching those behind Stuxnet, who did a good job covering their tracks.
While you shouldn’t be worried about your laptop getting a case of Stuxnet, the implications of industrial process monitoring machinery being hijacked and controlled by criminals are unthinkable. The methods the virus uses to spread, target, and control its victims are unprecedented and may be indicative of a new kind of terrorism: cyber-terrorism.
There are currently 441 nuclear reactors worldwide. If we assume that terrorists are able to control a quarter of these using industrial-targeting viruses, and they are capable of disabling temperature monitoring of the plants, terrorists could theoretically trigger 110 nuclear reactor meltdowns. If we assume statistics similar to the Chernobyl nuclear reactor disaster, each of these meltdowns could lead to more than 200,000 deaths in the long-term. These conservative estimates lead to a death toll of 20 million people worldwide as a result of the Stuxnet-enabled attack. A more widely targeted attack, or some bad meltdowns could easily inflate the death toll to 40 million or more. For purposes of comparison, if the largest nuclear bomb ever produced, the Tsar Bomba, were dropped on the most densely populated city in the world, Mumbai, the result would likely be less than a million deaths. Let’s hope that this is a trend that can soon be stopped. If not, it could lead to scenarios much more serious than the Y2K bug.